The Invisible Handshake: The Dead Computer Inside Your Credit Card
The anatomy of a "dead computer": Why your card wakes up for 500ms to negotiate the global economy.
You tap your card ten times a day without thinking about it. Beep. Green light. Done.
In the 500 milliseconds between tap and beep, a computer inside your card powered up from nothing, ran a cryptographic negotiation with the terminal, generated a one-time mathematical proof that it’s real, and powered back down. The whole sequence finished before you moved your hand.
Most people have done this thousands of times. Almost none of them know there’s an operating system inside the piece of plastic in their wallet.
Welcome to The Two-Second Swipe
This is the first installment of a six-part series that deconstructs the plumbing behind every card transaction. Over the coming weeks, we’re going to follow a single payment from the moment you tap to the moment cash lands in a merchant’s bank account, peeling back layers of infrastructure, economics, and quiet engineering brilliance along the way.
The Roadmap:
The Invisible Handshake (this one): The OS and one-time codes inside your card.
The 5,000-Mile Sprint: The 0.5-second game of global telephone.
The Rewards Tax: Why your “free” airline miles cost your coffee shop $0.15 per latte.
The Settlement: The 48-hour lag between the beep and the cash.
The Chargeback War: What happens when the “Approval” gets reversed.
The 50ms Mind: How AI guesses your identity before the beep.
Whether you’re a founder building a payments product, an engineer curious about the metal, or an operator trying to protect your margins, this is the map. Let’s start at the chip.
The Dead Computer
Your credit card contains a processor, ROM, RAM, and non-volatile storage (EEPROM), all packed onto a silicon die roughly 25 square millimeters. The size of a small fingernail. It runs its own operating system. And normally, it’s completely dead. No battery. No clock ticking. No activity of any kind.
The moment you insert or tap your card, the terminal’s electromagnetic field hits the chip’s antenna and induces a current. Power flows into a computer that, a fraction of a second ago, had none. The chip boots its OS, initializes its memory, and starts talking to the terminal.
This is electromagnetic induction, the same principle behind wireless chargers and electric transformers. The terminal is the power source. The card is the device. And the conversation between them is governed by a protocol called EMV, named after its creators: Europay, Mastercard, and Visa.
Why We Needed a New Card
To understand why the chip exists, you have to understand what it replaced.
In 1960, an IBM engineer named Forrest Parry was trying to attach a strip of magnetic tape to a plastic card for the CIA. The glue warped the tape and made it unreadable. His wife, Dorothea, was ironing clothes when he got home and told her the problem. She suggested he try the iron. The heat bonded the tape to the plastic without warping it. The magnetic stripe was born.
IBM standardized the technology in 1969 and gave it away for free, without filing a patent. By 1990, every dollar IBM spent developing the stripe had generated roughly $1,500 in computer sales. The stripe became the global default for decades.
Here’s the problem: a magnetic stripe is a recording. It stores a fixed set of data (your card number, expiration date, a static verification code) and plays that same recording every time it’s swiped. If someone copies the stripe, they have a perfect clone. Skimming devices attached to ATMs and gas pumps did exactly this, at industrial scale. By the early 1990s, card-present fraud was surging worldwide.
The EMV standard, created in 1994, was the answer. Instead of broadcasting a static number, the chip would generate a unique, one-time cryptographic proof for every single transaction. A proof that couldn’t be copied, replayed, or forged.
The concept landed in 1994. Europe and Asia adopted it within a decade. The U.S. waited 20 years.
The 20-Year Lag
Why did the United States drag its feet? Economics.
Upgrading every card terminal in the country cost real money, and under the old rules, banks absorbed the fraud losses, not merchants. Merchants had no financial incentive to upgrade their hardware. Banks ate the cost of counterfeiting because it was still cheaper than replacing the entire terminal infrastructure.
That math changed on October 1, 2015. Visa and Mastercard enacted the EMV liability shift: any merchant who hadn’t upgraded to a chip-capable terminal became liable for fraudulent swipe transactions. Overnight, the cost of inaction shifted to the party with the power to act.
Adoption exploded. By 2025, 96.2% of U.S. card-present transactions use EMV chip technology. Card-present fraud has dropped 87% since the chip rollout began.
The Handshake, Step by Step
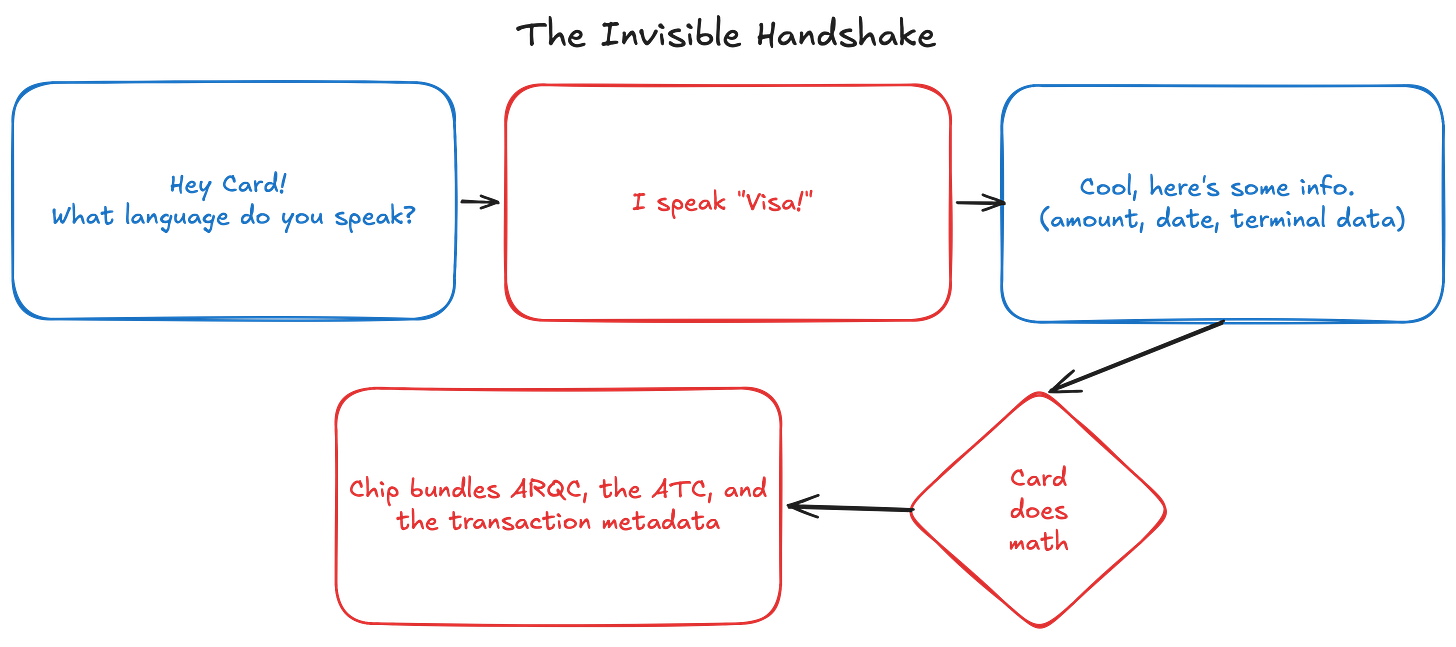
So what actually happens in those 500 milliseconds? Here’s the sequence.
Step 1: Card Selection. The terminal reads the chip’s Application Identifier to figure out which payment application to use (Visa, Mastercard, Amex). Think of it as the terminal asking: “What language do you speak?”
Step 2: The Challenge. The terminal sends the chip a package of data: a random number, the transaction amount, the date, and the terminal’s own identifier. This is the challenge.
Step 3: The Cryptogram. Here’s where the math happens. When your card was manufactured, a unique secret called the Master Derivation Key (MDK) was burned into the chip’s silicon. Your bank keeps a copy of this key. The chip never transmits it. Ever.
Each time you use your card, the chip combines its MDK with an Application Transaction Counter (ATC), a number that increments by one with every transaction, to derive a session key. The chip then takes that session key and runs it through a cryptographic algorithm (Triple DES or AES) along with the transaction data from the terminal’s challenge. The output is the ARQC: the Application Request Cryptogram.
The ARQC is mathematically bound to this card, this amount, this terminal, this moment. It will never exist again. If someone intercepts it and tries to replay it, the bank sees an ATC it’s already processed and rejects it instantly.
Step 4: The Package. The chip bundles the ARQC, the ATC, and the transaction metadata, and sends it all back to the terminal.
That’s the handshake. The terminal now has a sealed envelope of cryptographic proof. What happens next (the 5,000-mile relay through acquirers, networks, and issuers) is Part 2. But one more piece happens at this stage that most people don’t know about.
The Hidden Step: Bidirectional Authentication. When the bank eventually processes the ARQC, it doesn’t just send back “approved” or “declined.” It sends back its own cryptogram, the ARPC (Authorization Response Cryptogram), which the chip can verify. The card confirms that the response came from the real bank. Authentication runs both ways.
Why Interception Is Useless
The magnetic stripe’s fatal flaw was simple: copy it once, use it forever.
The chip flips that equation entirely. Every piece of data it produces is a one-time artifact. The ARQC is bound to a specific transaction counter. The session key is derived fresh each time. Even if an attacker captures every byte transmitted between your card and the terminal, they get a cryptogram that’s already been used, tied to an ATC the bank has already seen.
The chip also has a physical defense. Its surface contains a mesh of fine conductors called active shielding. If someone tries to probe the silicon with a needle or microscope to extract the MDK, the mesh detects the intrusion and the chip erases its own keys. It destroys the secret rather than let it be read.
Tap vs. Dip: Same Protocol, Different Radio
When you insert your card (the “dip”), the terminal’s metal contacts touch the chip directly and power it through physical contact. When you tap, NFC (Near Field Communication) replaces the metal contacts with a radio signal operating at 13.56 MHz.
The cryptographic protocol is identical. The challenge-response, the session key derivation, the ARQC, all of it runs the same way. The only difference is how the power and data reach the chip.
NFC operates at a practical range of about 4 centimeters. In academic settings, researchers have demonstrated passive eavesdropping at distances up to roughly 45 centimeters. But even a successful eavesdrop captures only the one-time cryptogram, which is worthless for replay. The short range is an intentional design choice, not a limitation.
Contactless transactions under $100 in the U.S. typically don’t require a PIN. The chip negotiates this with the terminal based on what’s called the Cardholder Verification Method (CVM). Below the threshold, the cryptographic authentication alone is considered sufficient. Above it, the terminal asks for a PIN (something you know) or signature (something you do).
Contactless also cuts transaction time. EMV dip transactions can take 2 to 3 seconds end to end. Contactless taps target sub-500 millisecond responsiveness at the terminal. That speed difference is why tap-to-pay has become the default at most retailers. Globally, about 80% of card transactions are now contactless.
Your Phone Has a Chip Too
When you pay with Apple Pay or Google Pay, the same EMV handshake runs. But the chip lives inside your phone, and the two platforms architect it very differently.
Apple’s approach: hardware isolation. Apple embeds a dedicated Secure Element, a tamper-resistant chip physically separated from the iPhone’s main processor. When you add a card to Apple Pay, the real card number never touches Apple’s servers. Instead, a token (a virtual card number called a Device Account Number) is created by the card network’s Token Service Provider and stored exclusively in the Secure Element. It’s never backed up to iCloud. It’s never synced across devices. If someone jailbreaks your iPhone, they still can’t reach it because the Secure Element has its own processor, its own OS, and its own cryptographic keys, all walled off from iOS.
Each tap generates a one-time cryptogram from the Secure Element, just like a physical chip card. The terminal sees a standard EMV transaction. It has no idea it’s talking to a phone.
Apple charges issuing banks 0.15% on every credit card transaction and $0.005 per debit transaction processed through Apple Pay. The fee is paid by the issuer, not the merchant or consumer. On billions of transactions, that’s a meaningful revenue line Apple has never formally broken out.
Google’s approach: software and servers. Google Pay uses a method called Host Card Emulation (HCE). There’s no dedicated hardware chip. Instead, the virtual account number is stored on Google’s servers, and a single-use token is generated at the time of each purchase and sent to the phone. The phone transmits that token over NFC, and the terminal processes it the same way.
Both produce the same output at the terminal: a one-time cryptogram tied to a unique transaction. The merchant can’t tell the difference. But the architecture underneath has a real distinction. With Apple, your credentials never leave your device. With Google, Google is in the middle. Neither approach has been meaningfully breached, but they represent two different bets on where security should live: in hardware you hold, or on servers you trust.
The Players: Who Built This Machine
The infrastructure behind a single tap involves three distinct layers: the standards body that writes the rules, the chip manufacturers that build the hardware, and the mobile wallet operators that repackaged the handshake for the phone era.
The Standards Body
EMVCo is the consortium that owns the EMV chip specifications, the tokenization framework, and the 3-D Secure standard for online authentication. It’s owned equally by six card networks: Visa, Mastercard, American Express, Discover (now Capital One), JCB (Japan), and UnionPay (China).
EMVCo itself doesn’t generate revenue. It’s shared infrastructure. But its owners benefit enormously: by setting the global chip standard, they’ve cemented their protocols as the default in over 100 countries. There is no competing payment chip standard at scale. Every terminal, every bank, every chip manufacturer conforms to EMV specifications.
The Chip Manufacturers
Four companies dominate the production of the silicon that sits inside your card.
NXP Semiconductors (NXPI) is a Dutch company and one of the largest makers of secure payment chips globally. NXP holds an estimated 20-25% share of the global smart card IC market. Total company revenue was roughly $12.6 billion in fiscal year 2024, with payment and security chips sitting inside its broader secure connected edge portfolio. In October 2025, NXP and Infineon formed a $180 million joint venture to build post-quantum secure elements, targeting production in late 2026.
Infineon Technologies (IFNNY) is a German semiconductor company and the other dominant force in payment chips. Also holding roughly 20-25% of the payment chip market, Infineon is the global leader in hardware security modules. Total company revenue was approximately €14.9 billion in fiscal year 2025. They’re expanding manufacturing capacity in Malaysia to serve growing Asian demand.
IDEMIA is a French identity and security company that both designs chips and manufactures finished cards (the company that prints your card and programs the chip). Its ID-One chip platform powers millions of payment cards globally. IDEMIA partnered with GlobalFoundries to build a 28-nanometer post-quantum-ready payment chip, with mass production targeted for 2026. In December 2025, they won a contract to supply 150 million biometric payment cards to India. IDEMIA is private, with estimated annual revenue of $2-3 billion.
Giesecke+Devrient (G+D) is a German company and one of the oldest card manufacturers in the world. They also print currency for central banks. Together with Thales, IDEMIA, Infineon, and NXP, they hold roughly 62% of the smart card market’s revenue. G+D is private, with estimated annual revenue of about €2.5 billion.
The broader market: the global smart card market is valued at approximately $16.2 billion in 2025, projected to reach $25.4 billion by 2032 at a 6.5% compound annual growth rate. Payment cards are the largest single use case, but government ID, transit, and healthcare cards are growing fast.
The Mobile Wallet Operators
Apple (AAPL) launched Apple Pay in 2014 and now operates one of the largest mobile payment platforms globally. Apple Pay is accepted at over 90% of U.S. retailers and leads the U.S. market by mobile transaction volume. Apple doesn’t break out Apple Pay revenue separately; it’s embedded within the Services segment, which generated $96.2 billion in fiscal year 2024. The 0.15% issuer fee on credit transactions, multiplied across billions of taps, is a revenue line Apple has never formally disclosed.
Google (GOOG) runs Google Pay through its HCE architecture. Google doesn’t charge issuers the same per-transaction fee Apple does. Its payments revenue model is less direct, tied more to transaction data and advertising adjacency. Google Pay holds a stronger position in Android-dominated markets outside the U.S.; domestically, Apple Pay leads by a significant margin.
What Happens Next
The terminal now holds the ARQC, the transaction counter, and all the metadata from the handshake. It’s ready to send this package out into the world: through the acquirer, across the card network, to your bank’s servers, where a fraud engine will analyze 2,000 variables in under 100 milliseconds before deciding whether to approve.
That sprint is Part 2.